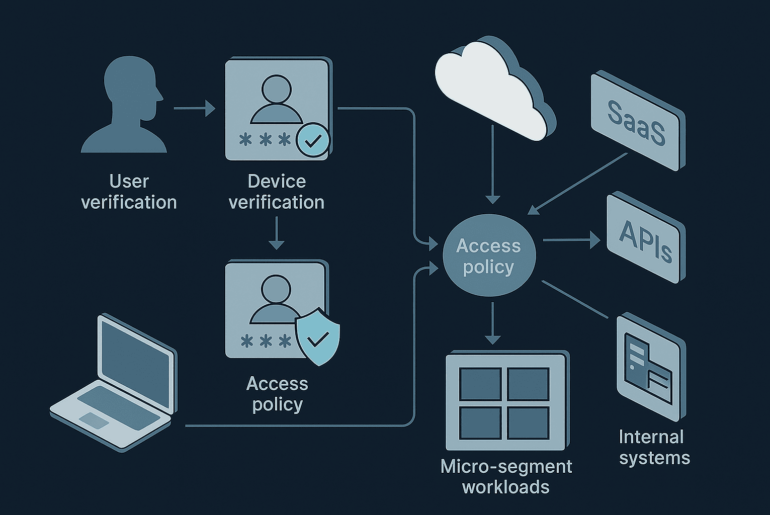
This Zero Trust implementation guide explains how organizations can build identity-first security in 2026—covering cloud, SaaS, APIs, and real-world execution challenges.
Cloud security failures rarely come from hackers alone — they come from misconfigurations, weak identity controls, and poor visibility. This guide explains real-world cybersecurity best practices for securing modern cloud systems.